Ethereum’s Vitalik Buterin Proposes ‘Stealth Address’ System to Enhance Blockchain Privacy – Here’s How it Works

Ethereum creator Vitalik Buterin has proposed a new “stealth address” system for Ethereum that would dramatically improve and simplify the workflow for achieving privacy for ordinary users.
According to a blog post published by Buterin over the weekend and titled An incomplete guide to stealth addresses, the proposed system would bring the same privacy properties as generating new addresses for each transaction someone receives.
The only difference would be that this would happen without any work needed for the receiver.
Privacy remains a large challenge on Ethereum
In the blog post, Buterin admitted that privacy – or the lack thereof – is a large problem for Ethereum users, saying:
“One of the largest remaining challenges in the Ethereum ecosystem is privacy. By default, anything that goes onto a public blockchain is public […] In practice, using the entire suite of Ethereum applications involves making a significant portion of your life public for anyone to see and analyze.”
He added that improving this situation for users is “widely recognized” as an important problem that developers should work on.
Secret spending keys and stealth meta-addresses
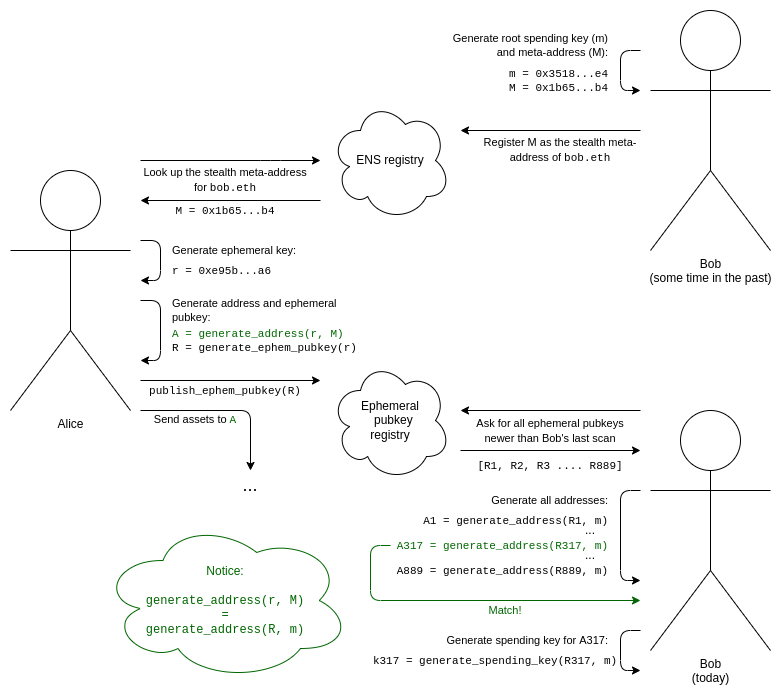
Specifically, the system proposed by Buterin would work by having wallets generate so-called stealth meta-addresses for receiving funds using a secret “spending key” that only the receiving party in a transaction has access to. The stealth address is then shared with the sender, who must also publish a piece of cryptographic data called an ephemeral pubkey on-chain for the receiver to understand that the address belongs to him.
To enable the generation of both the secret spending key and the public stealth meta-address, Buterin proposed to use a system known as the Diffie-Hellman key exchange. According to Buterin, this system is a foundational part of modern cryptography, and would accomplish exactly what is needed for stealth addresses to be implemented on Ethereum.
The Ethereum founder went on to share a detailed illustration of the workflow with the new system:
Zero-knowledge proofs
In conclusion, the Ethereum creator admitted that stealth addresses do introduce “some longer-term usability concerns,” including problems around so-called “social recovery” of lost keys. He said that these concerns could be simply accepted for now, but made it clear that a more lasting solution will likely depend “really heavily” on zero-knowledge (ZK) proofs.
- Strange New Chinese AI ‘KIMI’ Predicts the Price of Bitcoin by the End of 2026
- Sam Altman ChatGPT AI Predicts Wild Bitcoin Price by End of 2026
- You Will Not Like Where Google Gemini AI Predicts Bitcoin Going in The Next 30 Days
- Sam Altman ChatGPT AI Predicts XRP Price For The Next 30 Days
- Senate Returns With Clarity Act: CBDC Blocked, Stablecoins Win
- Strange New Chinese AI ‘KIMI’ Predicts the Price of Bitcoin by the End of 2026
- Sam Altman ChatGPT AI Predicts Wild Bitcoin Price by End of 2026
- You Will Not Like Where Google Gemini AI Predicts Bitcoin Going in The Next 30 Days
- Sam Altman ChatGPT AI Predicts XRP Price For The Next 30 Days
- Senate Returns With Clarity Act: CBDC Blocked, Stablecoins Win













