How To Store Cryptocurrency Safely in 2024
While it may initially seem daunting, storing your cryptocurrency safely is easier than it looks. However, safe crypto storage does require a more in-depth knowledge of crypto than simply acquiring it. This guide teaches you how to store your cryptocurrency safely, protect your crypto assets, choose the right wallet, and avoid the most common hazards of crypto security.
What Is A Crypto Wallet?
A cryptocurrency wallet is a software program designed to store your public and private keys, send and receive digital currencies, monitor their balance, and interact with various blockchains. You need to have a cryptocurrency wallet to manage your crypto assets and keep them secure.
There are many cryptocurrency wallets out there, but the essential distinction between them is whether they are hot or cold.
– A hot wallet is connected to the internet and can be accessed at any time.
– A cold wallet is not connected to the internet and allows you to store your funds offline. You can still receive funds at any time, but no one can transfer them out.
Hot wallets include all online cloud wallets, most mobile and software wallets, and exchanges.
Cold wallets are hardware wallets, offline kept paper wallets, USB and offline similar data storage devices, and even physical bearer items such as physical bitcoins.
Most cryptocurrency holders use both cold and hot wallets. Hot wallets are handy for frequent trading, while cold wallets are better for long-term holding of crypto assets.
But before we explore different wallets, here is a brief reminder of why keeping your digital assets in exchanges is generally not a good idea.
Types Of Cryptocurrency Wallets
There are five distinct categories of cryptocurrency wallets: paper, hardware, cloud, multi-signature, and online. Let’s have a look at each of them.
Multisignature Wallets
An increasingly popular solution, multi-signature wallets are an advanced way to keep your private keys securely distributed amongst different peers. It’s a top-notch security solution for businesses, family offices, decentralized organizations, and other individuals.
Multisignature vaults are a setup between multiple parties. For instance, you can set up a wallet that can be unlocked with 2-out-of-3 keys with your most trusted friends, family members, or business partners. This way, your funds are secure even if one of the keys is compromised or lost.
Understanding multisig security and setting up a multi-signature scheme can seem like advanced crypto knowledge, but it is getting easier over time as more tools become accessible to the general public. Many services often offer step-by-step video tutorials on how to set up such wallets.
If you’d rather not trust yourself to be the creator of your own multisignature scheme, there are numerous Bitcoin multisig services that seek to alleviate the trouble and pressure. If you’re interested in getting professional multisig assistance, please check out:
By combining cold storage and multisignature vaults, both individuals and companies can achieve an unprecedented level of security when it comes to keeping your crypto holdings safe and sound.
Paper Wallets
Paper wallets are generally classified as cold storage. The term ‘paper wallet’ generally refers to a physical copy or paper print of your public and private keys. Other times it means software used to generate a pair of keys along with digital file for printing. You can import your paper wallet into a software client or simply scan its QR code to move your funds.
Although paper wallets are cold, they are extremely risky and outdated technology. It is generally not recommended to keep large amounts of cryptocurrency on a paper wallet.
Cloud Wallets
Online wallets, by definition, are hot. Using a cloud wallet, your funds can be accessed from any computer, device, or location. They are super convenient, but they store your private keys online and can be controlled by third-parties. Therefore, they are more vulnerable to attacks and theft by design. Popular cloud wallets include:
- Guarda
- Coinbase
- Metamask
- Blockchain.info
A safer version of cloud wallets is non-custodial online wallets. They are accessible via web and apps but the service provider does not have access to your private keys. In most cases, not custodial wallets are a part of exchange platform, meaning that they let you trade your coins in a safe and secure manner. Examples of non-custodial cloud wallets include wallets by:
Software Wallets
Software wallets are downloaded and installed on a personal computer or smartphone. They are hot wallets. Both desktop and mobile wallets offer a high level of security; however, they cannot protect you against hacks and viruses, so you should try your best to stay malware-free.
As a rule, mobile wallets are way smaller and simpler than desktop wallets, but you can easily manage your funds using both of them. Besides, some software wallets allow you to access funds via multiple devices simultaneously, including smartphones, laptops, and even hardware wallets.
- Jaxx
- Freewallet
- Exodus
- Electrum Wallet
- Infino Wallet
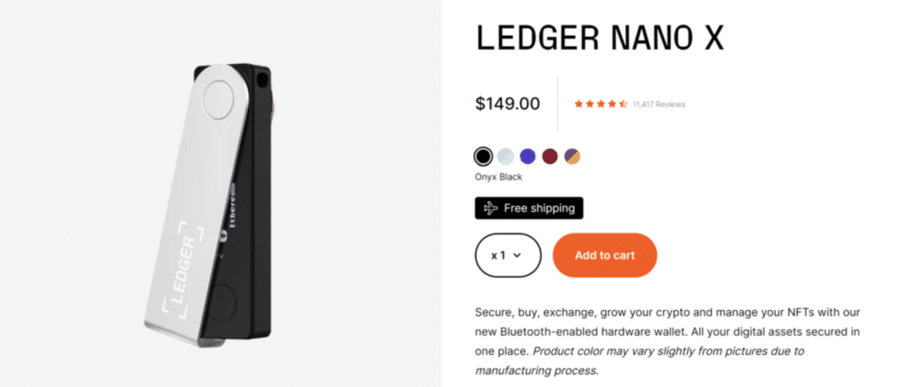
Hardware Wallets
Unlike software wallets, hardware wallets store your private keys on an external device like USB. They are entirely cold and secure. Also, they are capable of making online payments, too. Some hardware wallets are compatible with web interfaces and support multiple currencies.
They are designed to make transactions easy and convenient, so all you need to do is plug it in any online device, unlock your wallet, send currency, and confirm a transaction. Hardware wallets are considered the safest means of storing crypto assets. The only drawback is that they aren’t free to use.
Popular hardware wallets include devices by:
Getting a hardware wallet directly from a manufacturer is the most secure way. It is unsafe to buy it from other people, especially the ones you don’t know. Mind that even if you get a hardware wallet from a producer, you should always initialize and reset it yourself.
Typically, your wallet choice depends on your portfolio. Every serious project should have its native wallet, which should be found on its website, but sometimes it may be more convenient to have a multicurrency wallet.
Keep in mind that not all multicurrency wallets support all coins. Even hardware wallets have a limited amount of coins they support. On the other hand, there’s no shortage of wallets for popular cryptocurrencies like Bitcoin or Ethereum.
Once you get a (hardware) cryptocurrency wallet, you will also need to protect your private recovery seed phrase. One of the most reliable seed word protection tools is CryptoTag which allows you to store them on virtually indestructible titanium plates.

Best Security Practices to Prevent Stolen Private Keys
So you decided to take control of your crypto assets and hold everything in a private wallet. Well done! However, with great power comes great responsibility, and now it all rests on your ability to remain secure and keep your private keys private.
The most common security steps to take are:
- Don’t keep cryptocurrency in exchange for a prolonged period or longer than necessary.
- Always enable the two-factor authentication (2FA) function.
- If you go for a hardware wallet, choose a pin code that is hard to guess, and never put your 24-word recovery sheet online.
- Don’t boast of your crypto holdings publicly under your real name or identifiable address. Some burglars manage to steal crypto funds even if you keep them in cold (offline) storage.
- Trust only what you see on your hardware wallet screen and verify all the information on the device.
- Always assume that your devices can get compromised anytime, so always treat your computer or smartphone screen with caution.
In addition, follow these tips to minimize the chances of losing your crypto.
How to Keep Your Crypto Safe – Ultimate List
Be Aware Of Phishing Sites. Whether you’re connecting to exchange or online wallet, confirm that you’re logging in to the right address. Many bogus websites imitate exchanges for the sole purpose of stealing your login data. Always check whether the website address is correct.
Check That Websites are Secured With HTTPS. Log in only to secure websites with a valid HTTPS certificate. Most legit sites have one. For extra safety, try browser plugins like HTTPS Everywhere.
Use a Secure Wi-Fi Connection. Never connect to your online wallet, exchange account, or another critical security point via public WiFi. Even when you’re at a presumably safe place, make sure your WiFi access point uses strong encryption like the WPA-2 protocol.
Separate Your Funds. Don’t keep all your crypto assets in one place. The best way to handle it is by using one or several cold storages for long-term holdings and at least one hot wallet for trading and transactions.
Two-factor Authentication. Always secure your accounts with 2FA. Whenever possible, use software or hardware 2FA instruments rather than SMS.
Whitelist IP and Withdrawal Addresses. If you have a static IP address, use it for your safety. Make sure that only you can access your accounts and funds.
Double-check Crypto Addresses. Some malicious programs can edit and paste a wrong transaction address whenever you send a transaction. Typically, the new address belongs to an attacker. It’s better to be safe than sorry.
Use Security Measures You Can Handle. Some people never feel secure and go to the furthest lengths to secure their cryptocurrency. However, they forget that they can also lose crypto to their security tools.
Losing access to your accounts, funds, or wallets is as common as hacks. Don’t overcomplicate your security if that’s not what you’re into anyway. Strive for an appropriate balance between complexity and security.
The art of keeping your cryptocurrency safe and secure is a critical skill to master on a journey to becoming your own bank. The sooner you learn it, the better.
You may also be interested in – Guide: How to pick the best cryptocurrency exchange?
Conclusion
Storing cryptocurrency securely demands a multifaceted approach. You should use hardware wallets for offline storage, employ multi-signature wallets to distribute trust, and consider cold storage methods like paper wallets or offline hardware devices. Additionally, you should regularly backup private keys or seed phrases in secure locations, keep software updated, and implement strong passwords and encryption.
Phishing attempts and scams are very common in the crypto world, so make sure you diversify storage methods, and stay informed about evolving security practices and threats. By sticking to these principles, you can protect your cryptocurrency holdings from theft, loss, and unauthorized access.
How to Safely Store Cryptocurrency FAQs
How do you store your cryptocurrency?
Cryptocurrency can be stored in hardware or software wallets. Hardware wallets is best for long-term holding. If you’re storing your crypto in a software wallet, choose one that has strong encryption features.
What is the safest place to keep your cryptocurrency?
Hardware wallets offer the highest level of security due to their offline storage and tamper-resistant features.
How do you hold crypto for long-term?
Opt for cold storage solutions like hardware wallets or paper wallets, ensuring offline protection for prolonged periods.
How do you store crypto in cold storage?
Transfer your cryptocurrency to a hardware wallet or generate a paper wallet with private keys kept securely offline, away from internet access.


 Michael Graw
Michael Graw 
 Eliman Dambell
Eliman Dambell 
 Eric Huffman
Eric Huffman