With its mainnet launch planned for early 2019, the IOST platform aims to take on both EOS and Ethereum with the help of technologies focused on delivering fast TPS rates and creating a fully scalable and secure blockchain.

The Internet of Services (IOS/IOST) platform was built around a seemingly simple idea: blockchain technology can become the foundation of the decentralized economy if it focuses its use on the provision of online services. Yet, having access to blockchain is not a cure-all solution for the online service providers just by itself. It first needs to deal with some of existing technical issues and the IOST’s solutions to these are presented as its main benefits as well:
- IOST Plans to Make Blockchain Truly Scalable. Blockchain is gradually becoming a technological mainstream, leading to its higher adoption in various verticals. Yet, its speed is negatively impacted by the rise in the number of users, causing the problems related to its capacity to process a higher number of transactions and other operations. The IOST platform emerged as a response to the scalability problem which it aims to tackle once and for all. To that effect, it implements an array of technologies, including the distributed sharding technology, Proof-of-Believability algorithm and Micro State Blocks technology, all of which are supposed to offer higher TPS rates.
- IOST Aims to Have a Lighter Blockchain. Effective use of blockchain does not stop at resolving the scalability conundrum. The IOST team wants to make it more efficient, faster and leaner in its demand for storage capacity, processing power and configurations. This is to be achieved with the help of the Micro State Blocks and the faster implementation of the Byzantine Fault Tolerance mechanism.
- IOST Wants to Combine Accessibility with a User Reward System. With the IOST platform, its developers want to create and offer a transparent and permissionless system built on the open source principle. In theory, everyone should be allowed to take part in node running, transaction validation and access to services, with no hidden or transparent requirements for it. In addition, the platform will keep track of the users’ behavior and reward them with tokens accordingly.
- IOST Goes For Security Paired with Decentralization. IOST implements Byzantine Shard Atomic Commit (Atomix) protocol for the prevention of double spend hacks and information manipulations. The platform aims to become a “truth machine” dedicated to the protection of the fungibility and immutability principles promoted by the original blockchain.
The IOST platform’s general approach to these issues is informed by the perception that it is the architecture of blockchain solutions which creates technological roadblocks, high fees, slow transaction processing etc. Even the solutions which are being implemented now are sometimes untested and only partial. IOST offers its own twist on things by creating an ecosystem that will support the provision and exchange of decentralized online services and digital assets, paired with the support for the large–scale deployment of decentralized applications (dApps).
Other promised features of the IOST include:
- Decentralized P2P hosting.
- Private transactions.
- Lighter infrastructure suitable for the use with portable devices.
- The system of rewards for the users with an outstanding reputation.
The IOST platform also wants to make itself suitable for the provision of services which involve larger customer bases. The goal is to eventually allow the IOST developers to create their own versions of the existing popular platforms for the provision of online services, while relieving the users from the grip of their monopolies and business models.
The IOST platform uses sharding concept to build its database infrastructure from the scratch. Sharding is the principle by which the network nodes are divided into groups in charge of validating an amount of transactions which is proportionate to their size. In other words, databases get divided into appropriate shards, with each of them featuring different portions of information, not unlike what is found with the torrent technology.
This approach is supposed to offer several benefits:
- IOST platform distributes its workload across nodes and keeps an eye on their general performance health. If a node is overburdened, the sharding system will pick another node to send a portion of incoming workload its way, allowing the IOST network to scale its performance with the arrival of the new nodes on it.
- Search performance on the network should improve, as the sharding allows for the reduction of the index size. This is achieved by changing the approach to the management of the database tables. These tables function as collections of data within a set format in a database, such rows and columns. With the sharding approach, each row or line can be broken and assigned to a dedicated server, allowing for faster searches.
- Simultaneous verifications of transactions are made possible by forming groups of nodes. This approach is supposed to increase the throughput of the IOST network, with plans to eventually go for up to 100,000 transactions per second.
- While each shard holds different information, there is no need for each node to store information on the entire blockchain history. This allows for the easier access to information which are distributed across nodes and indexed based on the library-like technique.
- The costs of running dapps for larger pools of users can be reduced in parallel with the development of the IOST network itself. As the platform grows to include more nodes, the more resources will be at its disposal, making it more affordable for running dapps in the long run.
In order for the sharding approach to actually deliver the above benefits, it is necessary to combine it with a protocol that can introduce order in the node selection process, the appointment of leaders and management of malicious nodes.
This is the task of the distributed randomness protocol (DRP), which creates random numbers in order to group nodes into shards, shifts nodes among shards and appoints leaders. For starters, it is useful to know that IOST nodes are divided into two groups:
- “First class” nodes, which retain fully functioning features.
- Simplified payment verification nodes, which are used to verify transactions only.
IOST wants to treat any smart device as a potential node, without the need for dedicated servers used to verify transactions. The DRP protocol is used to establish communication between clients and servers, while ensuring the randomness and transparency of the number assigning process. The protocol itself is divided into randomness generation and verification stages and runs as follows:
- The client initiates a protocol by sending a message to all the servers about a randomly generated grouping.
- Each server creates random input values and shares which are solely intended for the other members of the same group. It applies publicly verifiable secret sharing (PVSS) system.
- Encrypted shares with the non-interactive zero-knowledge proofs (NIZK) are sent to the client from all servers. The client can pick out server inputs from each group.
- After this, the servers decrypt and forward their shares to the client once the client gets a sign-off based on input values in the collective signature.
- The client combines the recovered group secrets and reveals the final random output.
In order for the DPR to work as intended, the network has to be free from malicious or dishonest participants/nodes whose numbers should not go over the predefined threshold. In order to reduce their negative impact on the IOST network, the system appoints the leaders based on the Omniledger and Algorand mechanisms. They “force” the elected leader to run the DRP protocol, unless they want to be removed from the network.
IOST’s Proof-of-Believability
The IOST platform features a consensus mechanism called Proof-of-Believability (POB). Based on it, all the nodes on its network are divided into two basic groups:
- “Believable” nodes. These nodes process transactions.
- Standard or normal nodes. These nodes validate and verify processed transactions based on their samples.
Picking the nodes which are tasked with processing transactions is a complex process which comprises checking a specific node’s score on the scale of its “believability”. The criteria used in this case involve:
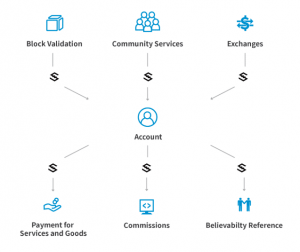
- The amount of Servi tokens a node has been awarded as part of the IOST’s reward system. These tokens are received whenever a user contributes to the IOST community voluntarily or provides evaluations of services provided by third parties. These tokens cannot be traded or exchanged and their balance goes back to zero once a block is validated.
- The previous behavior record of a node. IOST implements the reputation tracking and feedback monitoring system which is used to keep an eye on dishonest users whose behavior might hurt the network as a whole. Its Fair and Transparent Feedback System creates records of all user-based actions and interactions on the network and these data directly impact the user’s final believability score which is regularly checked.
- Token balance i.e. the amount of the IOST tokens in the node.
- The number of positive reviews of a particular node. This is supposed to incentivize users to act honestly on the network, even if they are largely anonymous.
The “normal” nodes serve as the watchdogs of the “believable” nodes in the sense that they monitor their behavior. In case the believable nodes are proven to exhibit dishonest behavior, their score is reset to zero and they lose all of their tokens.
What is the TransEpoch System?
The IOST platform implements the TransEpoch algorithm which maintains the Byzantine Fault Tolerance (BFT) consensus for each shard on it, and enforces the security of the platform. With this protocol, the malicious nodes are prevented to take over the shards when there is a transition between the epochs, i.e. time intervals. As the new nodes are downloading the information on history, the TransEpoch will ensure the regular operation of the remaining nodes which will proceed with the transaction validation during the transition.
What’s the Role of Atomix Protocol in IOST?
With sharding, making transactions across shards can be a complex process which can expose the platform to double spend attacks and proliferation of inaccurate data between the ledgers on each individual shard.
IOST implements the Byzantine Shard Atomic Commit (Atomix) protocol to protect itself from these potential security loopholes. For instance, these problems may arise when the users have two transactions taking place simultaneously and having an impact on each other, such as:
- Transfer XY amount of IOST from the address A to the address B.
- Check the token balance of the address A.
The Atomix protocol avoids the conflict by dealing with these events as a whole and combining all transaction steps across various nodes into a single, “atomic” unit. Even though the transaction is spread between various processing units, the results of each transaction have to be validated as error-free prior to the system allowing the transaction to take place.
How Does Micro Blocks Technology Work?
The technology of Micro State Blocks (MSBs) is one of the key elements in the IOST’s attempt to reduce the pressure on storage resources and shorten the time needed for the transaction processing. While having the nodes store entire ledger on the blockchain can be beneficial for protecting the system’s security, it can eventually become a performance obstacle as the ledger grows in size and more transactions take place onchain.
Instead of this, IOST’s Micro Blocks ensure that each shard exclusively stores only the headers from the previous blocks. Based on this, the nodes are required to validate only the final part of the chain instead of having to go through its entirety, and the blockchain’s state remains dispersed across the shards. This allows for the reduction of the block sizes, with each node being allowed to process only a certain segment of the network.
IOST Token Availability
The IOST token serves as the main exchange token on the IOST network. It is awarded for the validation of transactions and the contribution in computing resources for the provision of services, such as smart contracts.
The ICO for IOST was completed in January 2018, during which the total of 21 billion IOST tokens was minted. Of these, 12 billion tokens were in circulation as of January 2019. In the same period, the token’s market cap stood at USD 86 million, down from the peak cap of 816 million it had immediately after the ICO.
IOST tokens are available for purchase on crypto exchanges such as Binance, Huobi, KuCoin and others. Once acquired, the token may be stored in any ERC20-compatible wallet, at least until the mainnet’s official launch and the creation of an official IOST wallet.
IOST Team and Progress
The IOST platform is a China-based project headed by the 50-member team of professionals. Notable team members include Jimmy Zhong (CEO), Terrence Wang (CTO), Justin Li (CIO) and others. The majority of the IOST team members have backgrounds in the blockchain technology, IT and finances. The IOS Foundation was founded by Zhong, Wang and Li in order to promote the IOST platform as the proposed approach to the utilization of blockchain and dApps, particularly in business applications.
In advance of its mainnet launch in February 2019, the IOST ecosystem has drawn investments from various partners, such as the Pioneer fund which supported the development of projects on this platform. It remains to be seen how well the IOST will be able to compete with the likes of Ethereum, EOS, NEO, ICON and Lisk, which also present themselves as robust dApp platforms and offer their own solutions to the issues of blockchain scalability and corporate implementation.
