The cryptocurrency market is highly saturated with altcoins, diverse in their vision, utility and potential. Among them, Monero (XMR) stands out as an anonymous, privacy-focused digital cash.
The creators of Monero set out to address the privacy issues that arose with some of the first blockchains, such as Bitcoin and Ethereum; prioritizing users’ anonymity by operating outside the typical blockchain transparency ideal. Instead, the Monero blockchain and its XMR token facilitate anonymous transactions that make it difficult to trace or identify users.
So, what is XMR, and what should potential investors know about it? Our detailed guide will help you find out.

Monero Price
When reviewing Monero’s market performance, refer to its utility token, XMR. Just like most cryptocurrencies, XMR has been the subject of unpredictable price movements, but looking at market history can offer potential investors deeper insights into the value of the project.
The Monero price today (as of February 2024) is around $140 per token. The current XMR price is down by around 15% compared to its February 2023 price.
Monero has had an impressive run in the crypto market. In May 2021, the coin recorded an all-time high of over $470. Although the coin’s price has fallen significantly since then, market analysts predict a potential rise in Monero’s price will correlate with an increase in demand for anonymous financial technology.
Similarly, a potential resurgence in the broader crypto market post Bitcoin-halving in 2024 and beyond will potentially influence the price of Monero to rise. This being said, Binance announced a delisting of Monero in February 2024. This news, from such a reputable and widely-used exchange, will not only make investing in Monero less accessible, but is likely to negatively impact Monero’s price.
Factors influencing Monero’s price
Consider other factors which may contribute to XMR’s price movement:
- Market sentiment: Price action in the crypto market tends to be influenced by the general market sentiment, particularly Bitcoin sentiment. A positive outlook among traders and investors can cause a spike in the XMR price. Conversely, negative news can cause a decline in investor confidence, resulting in a price decrease.
- Demand and supply: Like other cryptocurrencies, supply and demand dynamics impact the price of Monero. Increasing demand will likely result in increasing prices, and vice versa.
Monero market performance
Analyze Monero’s market performance to determine whether XMR is a good investment. Ultimately, you can make informed decisions based on the information provided.
As of early February 2024, Monero’s trading price was around $168 per token. Monero has a market capitalization of about $3.07bn, so it is well positioned among the top 30 cryptocurrencies by market cap, as listed by CoinMarketCap.
Considering the thousands of cryptocurrencies in existence, Monero is well-positioned as a popular altcoin. However, its market cap is significantly lower than Bitcoin and Litecoin, (over $840bn and $5bn, respectively), which operate with the same PoW consensus model and intention to facilitate private transactions. Nonetheless, Monero remains one of the most traded cryptocurrencies, and its support for faster and cheaper payments than competing blockchains makes it valuable.
What is Monero (XMR)?
What is Monero? Monero is an open-source cryptocurrency network designed to provide users with privacy during transactions. Unlike mainstream blockchains, such as Bitcoin and Ethereum, Monero is intentionally built to prioritize user privacy by facilitating untraceable transfers.
While the Bitcoin blockchain makes all transaction details publicly available, when utilizing the Monero network, a user’s personal details (including the identities of both sender and receiver, as well as transaction amounts) are kept confidential.
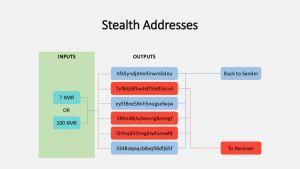
The Monero ledger is deliberately opaque, ensuring that actual wallet addresses of transacting parties are not recorded. Monero achieves this anonymity by rerouting coins through randomly created addresses specific to each transaction. This one-time created address is not linked to either party, making it challenging for anyone to trace addresses or individuals involved in a transactions.
But, what’s a Monero coin? The Monero (XMR) coin is the blockchain’s utility token that is used for various activities within the Monero network, including making anonymous, fast and cheap digital payments.
How does Monero work?
Monero sets itself apart from other blockchains with its focus on anonymity. Consider exactly how this is achieved by looking at XMR’s operational mechanisms.
User anonymity
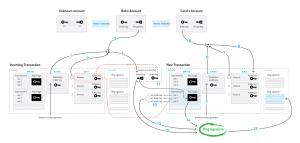
Transactions on the Monero blockchain are not transparent. The Monero blockchain uses a feature known as the ‘ring signature’, which decrypts the amount involved in any transaction, and ensures that each transaction is combined with multiple other transactions. By mixing one user’s funds with a whole group of other users’ funds, the source of funds for any one transaction is incredibly difficult to trace.
Monero also splits every individual transaction into a set of multiple, smaller transactions and treats each of these separately, making it practically impossible to determine the make-up of any one transaction.
For instance, to anyone looking, address A. sending $500 of XMR to address B. in one transaction would appear as though:
- Address C. had sent $150
- Address D. had sent $30
- Address E. had sent $20
- Address F. had sent $300
Proof-of-Work consensus mechanism
To validate transactions, Monero uses the Proof-of-Work (PoW) consensus mechanism, much like Bitcoin. This means that miners verify transactions on the blockchain.
Crypto mining
The Monero mining process follows an egalitarian ideal, meaning all miners are equal. Instead of a few miners with more sophisticated devices acheiving a bigger share of the mining rewards, investors are allowed to mine Monero using their own CPUs. That way, in order to mine Monero, there is no need to purchase expensive hardware or make a payment to join mining pools.
Off-chain governance
Diverting from the standard governance approach within the crypto arena, Monero’s governance occurs off-chain. To further enhance the community’s egalitarian nature, the external community makes decisions about the future of the project, as opposed to governance facilitated only by XMR token holders.
Use cases and application of Monero
Due to its anonymity, Monero is fit to serve many purposes, including:
- Anonymous donations and fundraising.
- Protecting corporate transaction history.
- Traceless trading and investment activities.
Naturally with anonymity, there comes the potential for illegality. Monero has been the subject of various underground activities, too.
Who created Monero?
Monero’s history dates back to 2013, when Nicolas van Saberhagen introduced the CryptoNote protocol as a blockchain platform to enable anonymous and decentralized cryptocurrency transactions.
A year later, Riccardo Spagni founded Monero, adapting CryptoNote’s blockchain model. Launched in April 2024 as a grassroots movement, Monero emerged as a fork of Bytecoin.
How to buy and store Monero
To buy Monero, investors should use a crypto exchange. These function much like traditional brokerage platforms, providing a way to buy, sell and speculate on cryptocurrencies.
Centralized crypto exchanges are managed by a third-party intermediary. A user need only create an account, fund it with a deposit, select the amount of XMR they want to buy, and confirm the purchase.
XMR can also be purchased on decentralized exchanges (DEXs) – DeFi-based instruments that distribute verification powers to those who help to secure the network and validate transactions.
Wallets and Chainlink safe storage
After buying XMR, it is important that coins be securely stored in a wallet.
No one wallet is fundamentally better than another. Hot wallets present the advantage of easy access and proactive management of cryptoassets, while cold wallets offer more long-term security. Non-custodial wallets will offer users increased control over their XMR, whereas custodial wallets that offer third-party support can be more beginner-friendly.
Review each wallet type and choose the one that best suits your needs.
Risks and challenges of investing in Monero
Like other cryptocurrencies, investing in Monero comes with significant risks:
- Volatility: Investing in Monero is risky due to the extreme volatility of the crypto market. Despite the possibility of the XMR’s price going up, investors should be aware of the possibility of losing the value of their entire investment in unfavorable market conditions.
- Criminal activity: Monero’s extreme privacy features can make it attractive to criminals and other malicious actors. As a result, the blockchain and its token are frequently banned by governments and cryptocurrency exchanges. For instance, the coin is banned in the UAE, and popular exchanges such as Coinbase and Binance have announced delistings.
- Market sentiment: Further negative sentiment about the coin being linked to criminal activities can negatively impact the project and its coin value.
- Limited utility: Finally, Monero’s real-world utility is limited, revolving only around payments as opposed to projects. Compared to other blockchains such as Ethereum and Solana, which support developers by facilitating the creation of decentralized apps (dApps), Monero’s limited utility may hinder the project’s future potential.
Regulatory and legal aspects of XMR
Although Monero prides itself on being a digital privacy coin, it faces various regulatory challenges.
Many countries have anti-money laundering laws mandating financial institutions and crypto exchanges to verify clients’ identities when trading digital currencies. This is to prevent criminal activities and other illegal uses of funds, such as terrorism financing. As a result, some countries have banned the use of Monero’s payment services in their financial institutions.
Also, some tier-1 exchanges such as Binance and OKX have delisted Monero because of the EU’s Fifth Anti-Money Laundering Directive (5AMLD) mandating client identification.
While Monero strives to comply with the laws in supported regions, regulatory and legal threats remain valid concerns for investors and the project as a whole. With fewer traders on major exchanges and a decline in investors’ confidence, the coin may face liquidity issues and lose value.
Comparing Monero to other cryptocurrencies
When compared with other top cryptocurrencies, including Bitcoin, Ethereum and Polygon, how does Monero fare?
Monero vs Bitcoin
The Bitcoin and Monero blockchains operate similarly using PoW consensus, requiring miners to validate transactions. Also, both platforms offer decentralized and open-source networks for investors. However, Monero offers more speed and scalability, making its transactions faster and cheaper than Bitcoin. On the other hand, Bitcoin is a better store of value, while Monero is a privacy coin for anonymous digital payments.
Monero vs Ethereum
Monero and Ethereum are built to boost scalability, flexibility and security. However, they differ in structure. Ethereum operates using the Proof-of-Stake (PoS) consensus mechanism, which validates transactions using smart contracts, while Monero uses PoW and miners. Similarly, Ethereum’s primary focus is to support other crypto projects such as dApps, while Monero is a privacy-focused blockchain.
Monero vs Polygon
Polygon and Monero were developed for similar purposes – to facilitate faster and cheaper transactions than Bitcoin and Ethereum. They were also aimed at solving the scalability issues that Bitcoin faced. However, the Polygon blockchain is transparent, while Monero is obscure. Similarly, Monero has an average transaction time of two minutes, while a Polygon transaction takes about two seconds to confirm.
FAQs
How much is 1 Monero?
At the time of writing, one unit of XMR is around the $168 mark. At this time, the coin was experiencing a market uptrend, causing an optimistic Monero price prediction among market analysts.
Is Monero illegal?
Despite its various regulatory challenges due to its privacy focus, Monero is not illegal. However, its transactions are not traceable, so some countries prohibit its usage and trading.
Is Monero a good investment?
Monero may be a good investment for short- and long-term traders. Mining Monero doesn’t require expensive hardware as it can be done through a computer’s GPU/CPU.
